Case Study: Oracle Roving Edge Device — Cloud Console for Defense-Grade Edge Computing
Built and maintained the operator-facing cloud console for Oracle's Roving Edge Device — ruggedized, portable hardware that brings full OCI compute, storage, and AI/ML capabilities to disconnected and classified environments. The console I worked on is the interface defense and enterprise operators use to provision, manage, and monitor edge infrastructure deployed in the field.
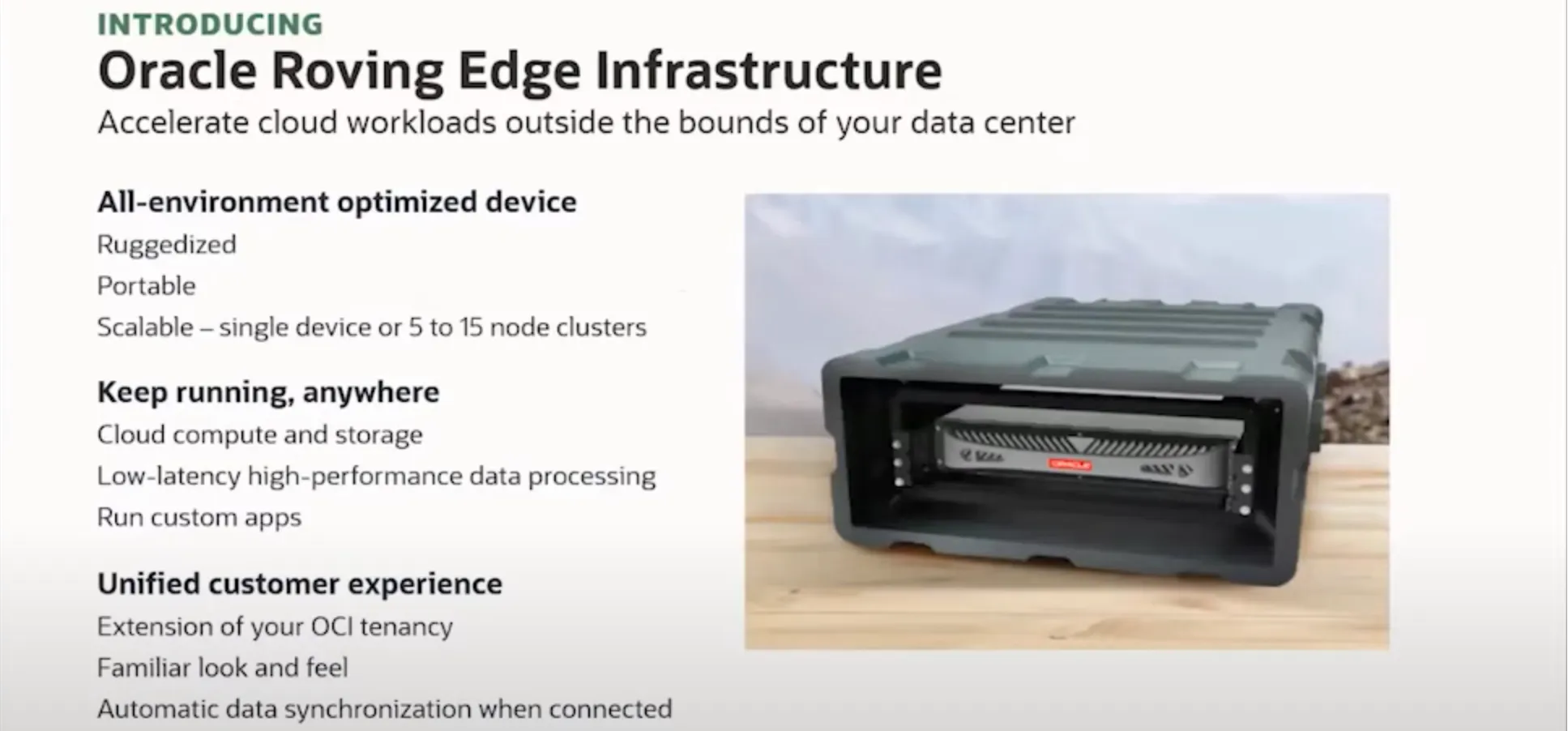
The Product
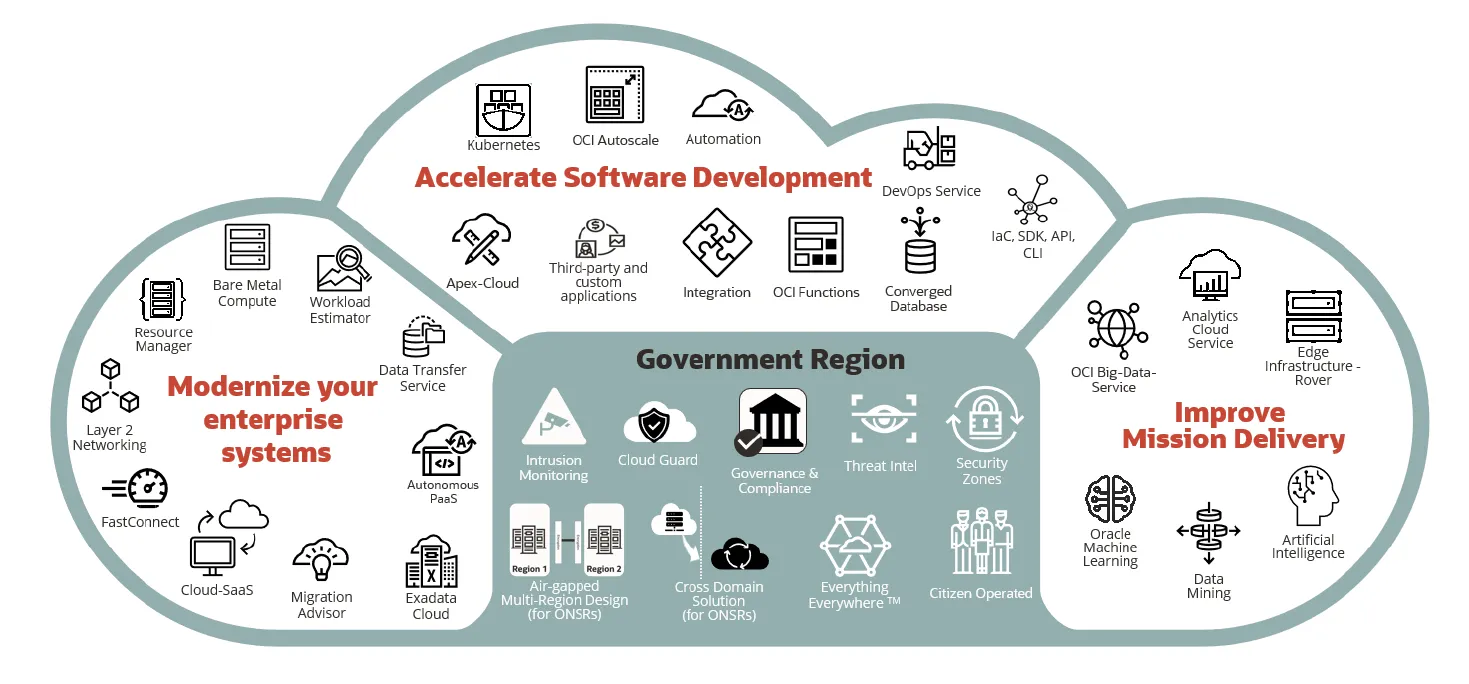
The Oracle Roving Edge Device (RED) is a portable hardware platform that runs the same OCI cloud services — compute, storage, networking — at the edge of networks and in fully disconnected locations. It's built for environments where latency, data sovereignty, and physical security matter: forward operating bases, remote government facilities, tactical military vehicles, and industrial sites with no reliable connectivity.
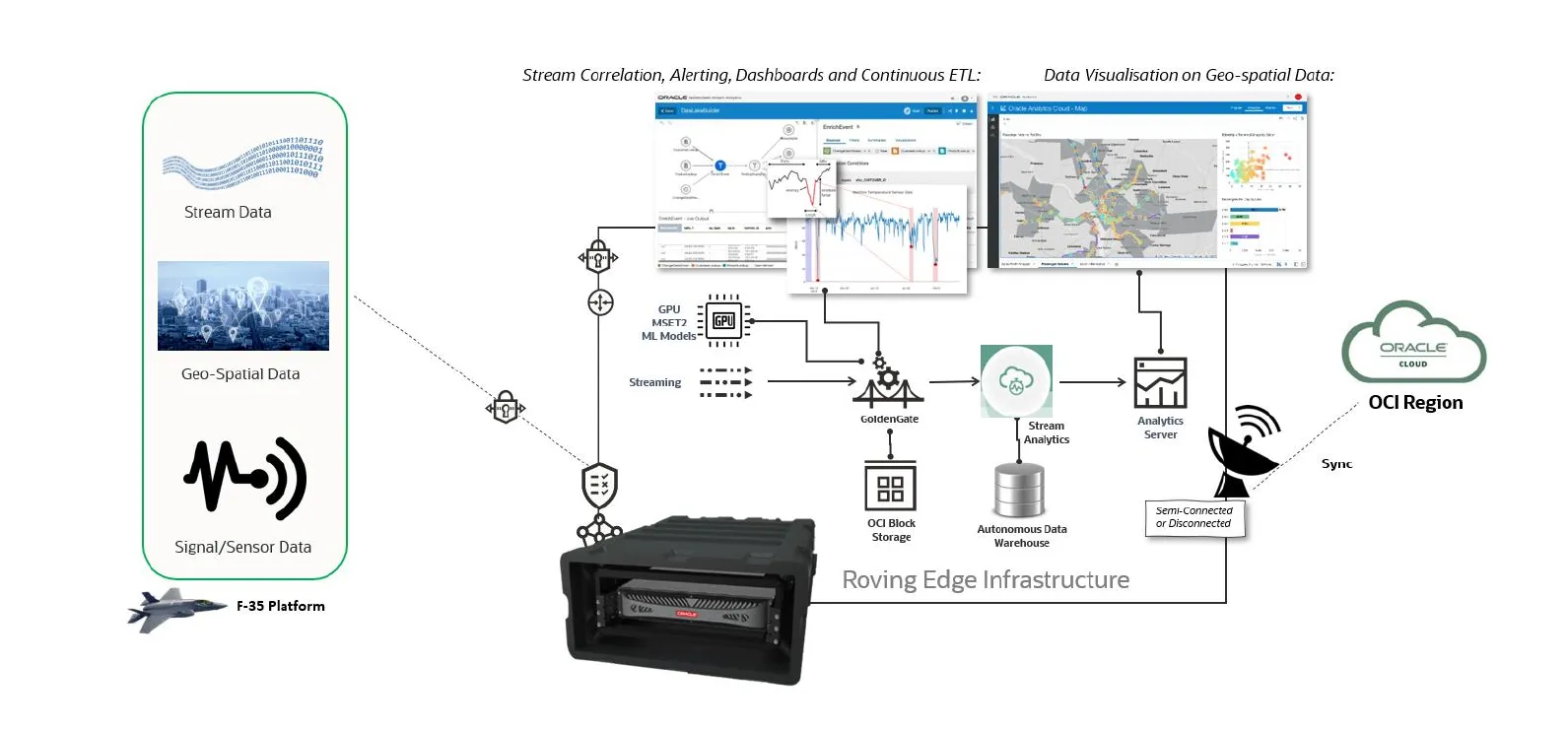
The 2nd generation RED ships in three configurations, including a GPU-optimized variant with three NVIDIA L4 GPUs for running AI/ML workloads — anomaly detection, threat identification, facial recognition, and video analytics — directly at the point of data generation. The device carries MIL-STD-810H (environmental), MIL-STD-461G (electromagnetic), and FIPS 140-3 Level 2 certifications. OCI holds DoD Impact Level 5 and FedRAMP High accreditations, and Oracle Cloud Isolated Regions support top-secret/SCI classified missions.
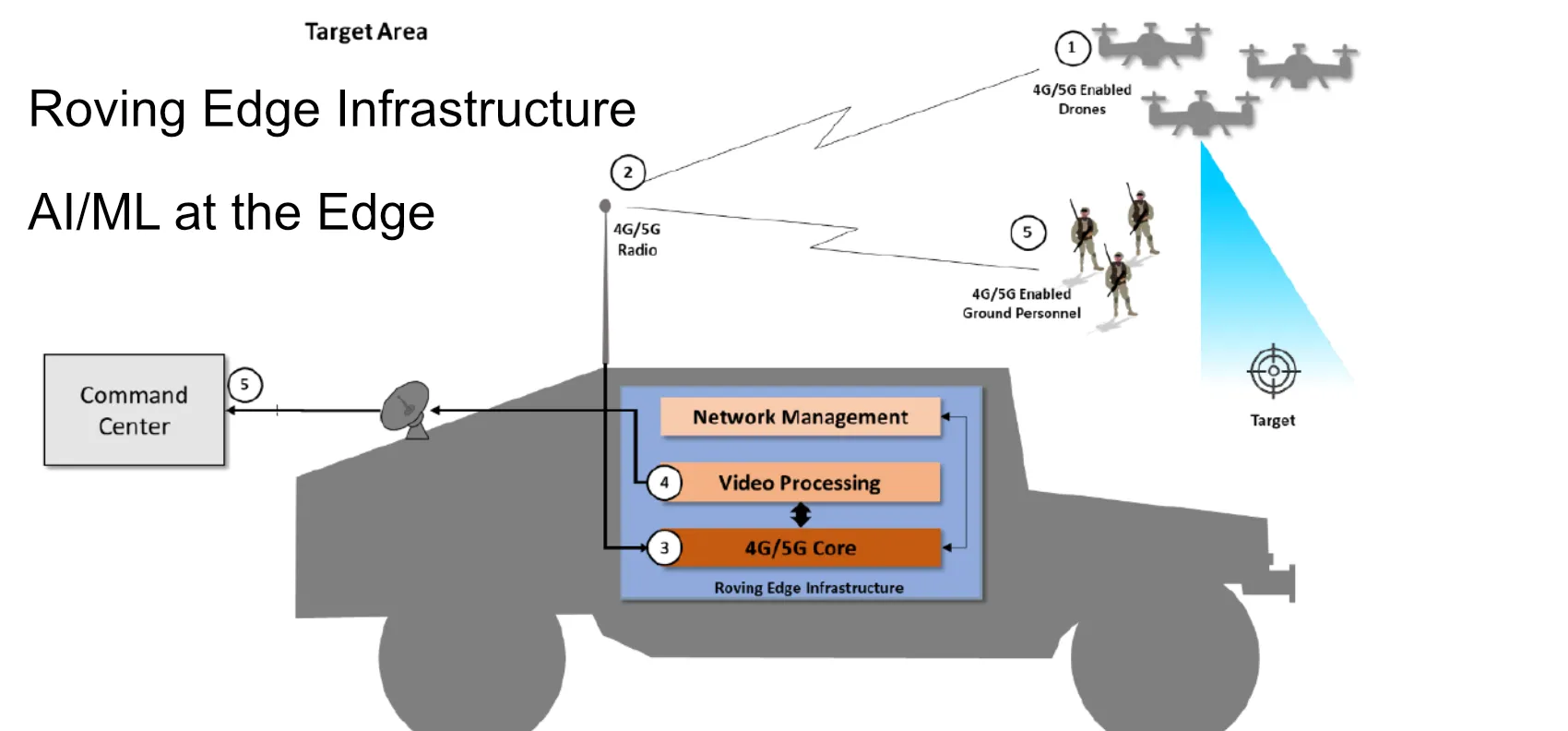
Real-world use cases include processing terabytes of F-35 sensor data on the flight line for real-time battlefield intelligence, and hosting tactical 4G/5G mobile networks on military vehicles for drone surveillance and AI-powered target identification in the field.
My Role
As a Software Engineer (IC2) on the OCI Roving Edge team, I worked on the cloud console — the web application that operators use to configure, deploy, and manage Roving Edge devices and the workloads running on them. This is the same interface used across OCI public cloud, Cloud@Customer, and edge deployments, so consistency, reliability, and accessibility are non-negotiable.
Frontend Architecture and Component Standards
OCI product engineering spans dozens of interconnected service teams, each shipping features into a shared console experience. When I joined, teams had uneven UI patterns and duplicated implementation effort across services. I defined frontend architecture standards — component patterns, data-fetching conventions, and documentation — that gave teams a consistent foundation to build on. The goal was fewer integration surprises and better defaults out of the box, so engineers could focus on their service logic instead of reinventing shared UI patterns.
Internal Tooling and Workflow Automation
I built internal tooling to automate infrastructure-related workflows that were previously manual and error-prone. These tools reduced setup time for new services and standardized processes that had been handled inconsistently across teams. This work directly improved engineering velocity — less time on boilerplate meant more time on features that shipped to customers.
Accessibility (WCAG Compliance)
Government and defense customers operate under strict accessibility requirements. I partnered with design and QA to implement WCAG-aligned usability improvements across customer-facing interfaces. This wasn't cosmetic polish — for a product serving federal agencies with Section 508 obligations, accessibility compliance is a gating requirement for procurement.
Onboarding and Developer Experience
I streamlined onboarding paths for new engineers joining the OCI console ecosystem. In a codebase this large, ramp-up time directly impacts team throughput. Clearer standards, better documentation, and reduced setup friction meant new contributors could ship meaningful changes faster.
Engineering Context
Why This Work Matters
The Roving Edge console isn't a typical SaaS dashboard. The operators using it may be provisioning compute for a classified air-gapped environment, deploying AI workloads to a device in a tactical vehicle, or managing storage synchronization between a disconnected edge node and a central OCI region. The interface needs to be reliable, accessible, and consistent with the broader OCI console — because the same APIs, CLI, and SDK that work in Oracle Public Cloud work identically on the Roving Edge Device. That consistency is a core product promise, and the frontend I worked on is where operators experience it.
Scale and Constraints
OCI's console serves hundreds of cloud services across public, government, and classified regions. Changes to shared patterns affect every team downstream. The key tension was introducing enough structure to improve quality and velocity without blocking domain-specific delivery needs — standardization in a large engineering organization requires earning adoption, not mandating it.
Outcomes
- Reduced engineering friction through targeted internal automation, eliminating manual steps in day-to-day workflows across OCI product teams.
- Faster contributor ramp-up through clearer architecture standards, better documentation, and streamlined onboarding paths for new engineers.
- Raised accessibility baseline in customer-facing interfaces through design/QA partnership — critical for government and defense procurement compliance.
- Foundation for IC3 scope — the standards and tooling I established directly enabled later work including AI-assisted setup automation on the OCI platform.
Product screenshots are from Oracle's public data sheets. Console UI is internal to Oracle.
Project information
- Category: Edge Computing / Defense Infrastructure
- Role: Software Engineer (IC2), OCI Roving Edge
- Employer: Oracle Corporation
- Timeframe: 2022 - 2024
- Technologies: TypeScript, React, Oracle JET, WCAG/Section 508, Internal Tooling, CI/CD
- Oracle Roving Edge Infrastructure
- Console UI is internal to Oracle.